Data Loss Prevention – DLP
What is DLP??
Data Loss Prevention – DLP, or data loss prevention solution is a set of solutions combining Software Tools and Regulations / Processes to ensure that data assets of organizations and businesses are not stolen. , leak or misuse, accidentally or intentionally by a user.
DLP identifies and classifies sensitive data, and tracks and detects violations of regulations promulgated by Organizations, businesses, or violations related to government regulations and some international standards such as PCI-DSS, HIPAA, GDPR, etc …
The DLP enforces data sharing and use regulations such as giving warnings and taking measures to prevent accidental data leakage, or intentional theft of data that exists. may lead to risks or damage to the Organization or enterprises.
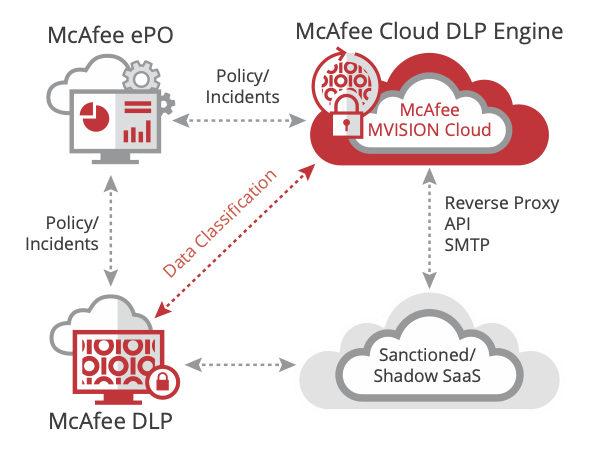
DLP can monitor and control activities on a user’s computer, monitor the flow of data sent over the network, scan storage folders to enforce data storage regulations, or control Use and share data on cloud applications like Office 365, One Drive, Gsuite, etc.
Main uses of DLP
DLP can help organizations and businesses solve three main problems:
- Protecting business data assets
- Get a clear picture of data usage and sharing within the business
- Meet domestic and international standards for data protection.
Protecting business data assets
Each organization or business has a lot of important data such as intellectual property, information about business secrets, customer databases, etc., which can cause loss or theft. significantly affect the image of the brand, the profit and the performance of the Company. DLP solutions provide protection of data types based on content and context, something conventional security solutions are difficult to achieve.
Get a clear picture of data usage and sharing within the business
Most organizations and businesses today have difficulty monitoring and controlling the use and sharing of Company data by employees because of the complexity of data and the diversity and diversity of data. Modern tools such as web application, chat application, email, cloud storage, etc. With a complete DLP solution, customers have the ability to observe and track all user usage and data sharing. right at their computers or controlled via network systems and cloud applications.
Meet domestic and international standards for data protection
Some organizations and businesses today, especially those working in the banking and finance sector or businesses with business activities related to foreign partners, all face very strong regulations. strict on the protection of customer information and data such as PCI-DSS, HIPAA, GDPR, etc … DLP is a solution that helps organizations and businesses can meet these strict requirements by Technical measures have been verified and widely used by major corporations around the world. DLP allows customers to define rules themselves or use existing rule sets that have been optimized for each standard to help customers save management time and increase efficiency in implementation. policy.
Strategy for DLP implementation
Define specific goals
The main goal of the Company Are you in need of protecting data assets, needing to see the use and sharing of data or need to meet a certain standard? Once you have identified a specific goal, in the next step, you will easily choose the right tools and models to deploy. There are typically four deployment models for a DLP solution, which businesses can do individually or in sync with each other:
- Control DLP deployment at user workstations.
- Deploy DLP monitoring over network channels.
- Deploy DLP to scan and scan data storage channels.
- Deploying DLP for cloud applications.
Share needs and responsibilities
The DLP is not a solution that only benefits the Company’s IT or security department, but involves all other departments and divisions as well. For example, the risk management department will need DLP to be able to evaluate and mitigate the impact of internal data leakage and leakage. The need to use the DLP and the responsibility in implementing the DLP relates to all parts of the Company, so it is important to define the right approach and clearly assign responsibilities in the implementation of the DLP project, including operation stage afterward.
Start with a simple script and easy to follow
Many businesses often find it difficult to start implementing DLP with a very complex plan or trying to solve many problems at once. You should try to identify your initial achievable goals in a quick and quantifiable manner. For example, you can narrow the scope and focus on controlling some specific data first and then replicate it. Or you will approach in the direction of scanning and classifying data on a large scale first then imposing control policy.
Work closely with the data owner.
To determine the rules that apply when controlling data sharing, it is important to coordinate with each data owner or with each department. It will help you to understand the very different needs between departments and data owners and the extent to which the DLP affects them. Usually the rules imposed on DLP go hand in hand with the strategic direction and culture of each Company.
Determine the success index and report it to the Company’s Board of Directors
Define clear KPIs when implementing DLP and follow them closely to quantify success and difficulties to overcome. Report these metrics to Company management so that they can assess the positive impact and economic value of DLP.
DLP is just a tool, a prerequisite, not a condition:
Equipping a DLP solution is just the first step in implementing data loss prevention. Once you have achieved your first success with a simple scenario, you will realize that the DLP is a tool that requires constant interaction in order to achieve overall success. DLP is a joint process that requires a combination of data understanding, understanding how technical tools work, and how users interact with the data, and with Company regulation to ensure that Data loss prevention is the most effective.
INFORMATION SOLUTION DISTRIBUTOR: