What is Endpoint Protection?
Endpoint Protection is the endpoint protection solution from cyber attacks, protecting computer systems from complex attacks or new generation attacks, which are exploited on many level of network infrastructure and have many serious consequences for individuals, businesses and organizations.
This software provides comprehensive security solutions for a wide range of customers from individuals to businesses (from small to large), government organizations around the world.
The necessity of an Endpoint Protection solution
According to the analysis reports of Gartner, IDG or Frost & Sullivan, the ―Endpoint terminals are always the weakest security weaknesses, vulnerable to attacks as well as the most hacked of most businesses. Karma. Therefore, there is a need to have a secure security solution to protect the weakest point within this system.
In terms of users, the terminal will include desktops, laptops / ultrabooks and portable storage devices – these are also the points that need to be protected because there are often many points. the weakest as well as the most attacked.
In addition, in a data center, from the server to the database, the storage device is considered a ― terminal and needs to be monitored and protected. These are all corrective devices but valuable information related to the network infrastructure of the business in particular or the business of the business in general, so there should be methods to ensure safety.
With more and more terminals connected to the system, businesses / organizations began to look for new ways to protect all of these devices in the direction of protecting all information at the same time. has the ability to optimize the most flexible and flexible way.
Technical features of Endpoint Protection solutions
The Endpoint Protection solution provides a security platform with many components working closely together to not only reduce the complexity of the endpoint environment but also increase security efficiency as well as provide an intuitive view. of threats to the system that happen every day so that administrators can easily and quickly respond to these threats proactively.
- Integrated with many security modules creates a multi-layer defense while still retaining the uniformity.
- Behavioral-based detection combined with machine learning provides more comprehensive protection than signature-based detection.
- Protect users from malicious code by detecting and blocking threats based on their behavior, thereby preventing the spread of malware to the whole system in which ransomeware is an example.
- Using intelligent data centers that contain threat intelligence modules can connect here to get information to help speed detection.
In addition, the solution can also be integrated with the EDR solution to increase resilience and adaptability, helping to eliminate threats from the system.
Therefore, Endpoint Protection solution ensures the following technical criteria:
Feature:
1 / Anti-malware:
Endpoint Security: Combines a variety of technologies to protect users’ computers in real time, analyze and detect new types of malware, advanced malware, and then stop them before they affect users. the whole system.
Dynamic Application Containment: Check behavior safely and prevent threats from greyware, ransomware, patient-zero threat, …
Real Protect:
Detect and block advanced, zero-day threats by analyzing real-time behavior combined with machine learning, extracting behavioral information before and after files execution and memory analysis to conclude.
Fight off sandbox-recognizable malware by allowing “malicious” behaviors to be executed, then analyzing them, combining with Dymanic Application Containment to control these malicious behaviors first. when they have the impact on the computer.
Host IPS: Protects device from security vulnerabilities, unknown and zero-day threat.
Threat Intelligence: Continuously update new malware samples and variants appearing globally.
2 / Web and Messaging Security:
Web control by URL filtering and Safe Search:
– Warn users about malicious websites before they visit to reduce risks and comply with regulations.
– Enforce policies that allow you to authorize or prevent web access.
Anti-malware and anti-spam for email:
– Protect email servers and prevent malware before they reach user mail box.
Detect, clean and prevent malicious code for Microsoft Exchange and Lotus Domino systems.
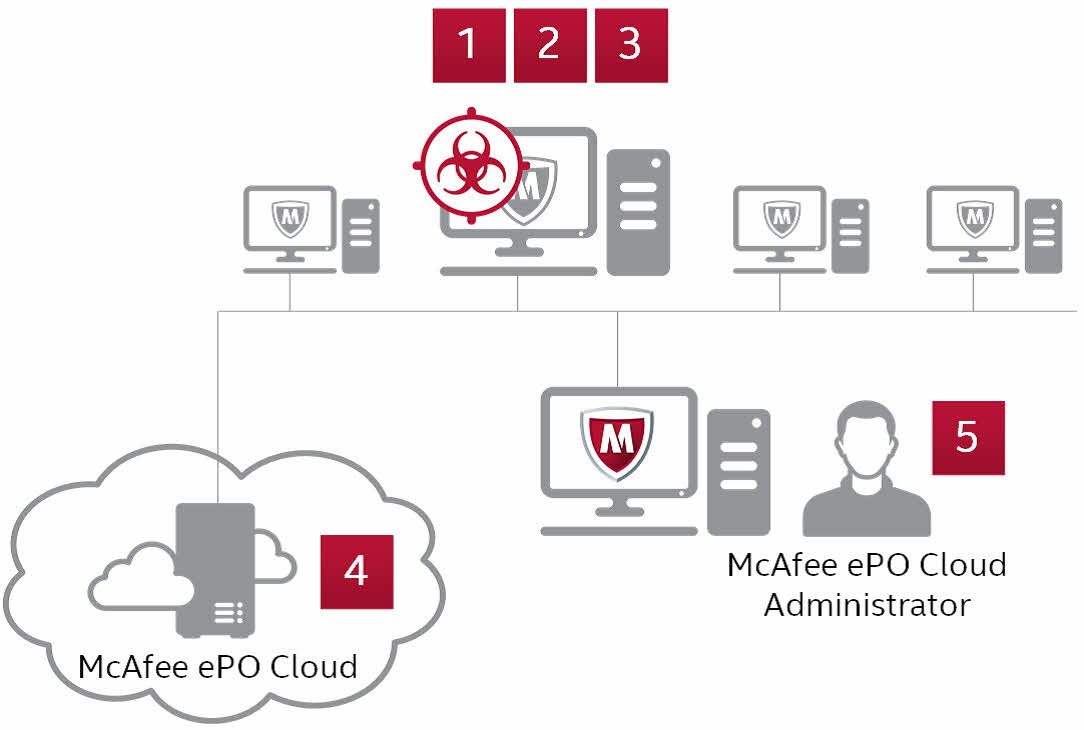
3 / Centralized Management:
Control policy, compliance, and reporting from a single monitoring and management interface.
Simplify managing many different OS environments with different policies.
(Important features of Endpoint Protection solution)
For more information about McAfee Complete Endpoint Protection products, readers (users), quickly FILL INFORMATION IN FORM REGISTER to receive FREE CONSULTATION from Viet Net Distribution Joint Stock Company.
Viet Net Distribution Joint Stock Company is the official Distributor of McAfee in Vietnam market – Top 1 in customer service.
INFORMATION SOLUTIONS PROVIDER: